Ah - thanks - I came back to answer this having got it working, and found it has already been answered!
Not sure what RADIUS server you are using - we are using Pulse Policy Secure. We are also using a Juniper EX4300 with Junos 17.3 - I think port-bounce was first introduced for this switch in 17.3.
The steps we took:
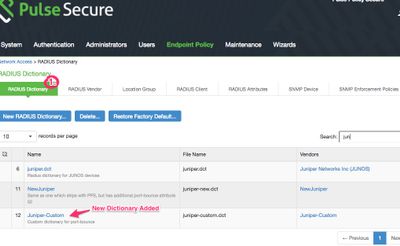
First, retrieve the Juniper.dct file from PPS under Endpoint Policy | Network Access | Radius Dictionary. Edit it to include the following at the bottom:
ATTRIBUTE Juniper-AV-Pair Juniper-VSA(52, string) r
1. Load it back into PPS using a custom name so you don't overwrite the original juniper.dct that came with the product. I called mine Juniper-Custom:
When you click it, you can expand the attributes and see Juniper-AV-Pair in there:
 Juniper-AV-Pair attribute in new dictionary
Juniper-AV-Pair attribute in new dictionary
2. Add a new 'Vendor' that references this new dictionary you just created:
 Adding a new radius vendor
Adding a new radius vendor
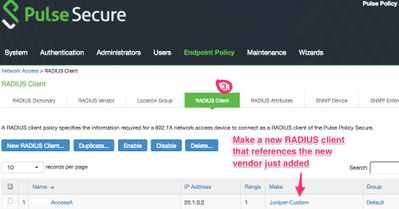
3. Change the RADIUS client (the ethernet switch) in PPS so that it uses this new vendor:
4. Under RADIUS Attributes, add the right return attribute and VLAN:
 Setting up the 'port-bounce' RADIUS return attribute
Setting up the 'port-bounce' RADIUS return attribute
5. Once complete, the screen should look like this:
 Completed return attribute
Completed return attribute
This seemed to work just fine. We get the COA messages in our debug as per the previous posting, and the device moves VLANs.
Good luck,
Andrew