I am having trouble with Dynamic VPN IPsec Juniper SRX , Dynamic VPN IPsec was successfully created but cannot ping other segments' ip, how to solve it? can't ping segments on the vpn dynamic client 192.168.3.0/24, 192.168.2.0/24, 192.168.1.0/24, 10.10.10.0/24
"configuration"
security {
ike {
policy ike_pol_wizard_dyn_vpn {
mode aggressive;
proposal-set basic;
pre-shared-key ascii-text "?"; ## SECRET-DATA
}
gateway gw_wizard_dyn_vpn {
ike-policy ike_pol_wizard_dyn_vpn;
dynamic {
hostname SRX;
connections-limit 50;
ike-user-type group-ike-id;
}
external-interface ge-0/0/0.0;
aaa {
access-profile remote_access_profile;
}
}
}
ipsec {
policy ipsec_pol_wizard_dyn_vpn {
proposal-set basic;
}
vpn wizard_dyn_vpn {
ike {
gateway gw_wizard_dyn_vpn;
ipsec-policy ipsec_pol_wizard_dyn_vpn;
}
}
}
}
dynamic-vpn {
access-profile remote_access_profile;
clients {
wizard-dyn-group {
remote-protected-resources {
192.168.3.0/24;
192.168.2.0/24;
192.168.1.0/24;
192.168.0.0/24;
10.10.10.0/24;
}
ipsec-vpn wizard_dyn_vpn;
user {
srxuser2;
}
}
}
}
}
access {
profile remote_access_profile {
client srxuser2 {
firewall-user {
password "?"; ## SECRET-DATA
}
}
address-assignment {
pool dyn-vpn-address-pool;
}
pool dyn-vpn-address-pool {
family inet {
network 10.20.30.0/24;
dhcp-attributes {
name-server {
192.168.0.1;
192.168.0.11;
1.1.1.1;
}
router {
192.168.0.8;
}
}
xauth-attributes {
primary-dns 192.168.0.11/32;
}
}
}
}
firewall-authentication {
web-authentication {
default-profile remote_access_profile;
}
}
}
root@SRX# show security policies
from-zone untrust to-zone trust {
}
policy policy_in_wizard_dyn_vpn {
match {
source-address any;
destination-address any;
application any;
}
then {
permit {
tunnel {
ipsec-vpn wizard_dyn_vpn;
}
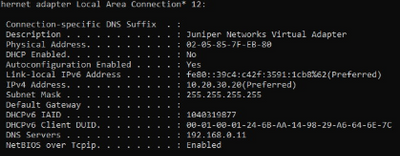
ip obtained by the client