Hi experts, I am going to test IPsec VPN with PKI Certificate Authentication, but failed in IKE P1:
Topology:
PicoRBS ---------------Transmission Network----------------SecGW(SRX3400 Cluster)
IKE Remote:10.185.49.194 (/29) ------------------------------------------------------------IKE Local:10.185.49.212 (/29)
Days ago, I have successfully established IPsec P1/P2 with PKI Authentication and Static IKE Peer, but when I configure with Dynamic IKE Peer, there is a failure.
Errors:
********************************
ike traceoption
[Apr 14 02:26:00 PIC 1/7/0 KMD1]iked_pm_ike_spd_notify_received: Received Unauthenticated notification payload NAT detection destination IP from local:10.185.49.212 remote:10.185.49.194 IKEv2 for P1 SA 1887121709
[Apr 14 02:26:00 PIC 1/7/0 KMD1]iked_pm_ike_spd_notify_received: Received Unauthenticated notification payload Multiple auth supported from local:10.185.49.212 remote:10.185.49.194 IKEv2 for P1 SA 1887121709
[Apr 14 02:26:00 PIC 1/7/0 KMD1]ikev2_decode_packet: [100f92000/100fc7800] Received packet: HDR, SA, KE, Nonce, N(NAT_DETECTION_SOURCE_IP), N(NAT_DETECTION_DESTINATION_IP), CERTREQ, N(MULTIPLE_AUTH_SUPPORTED)
[Apr 14 02:26:00 PIC 1/7/0 KMD1]ikev2_packet_allocate: Allocated packet 100f77800 from freelist
[Apr 14 02:26:00 PIC 1/7/0 KMD1]Added (spi=0xe2ea7cb, protocol=0) entry to the spi table
[Apr 14 02:26:00 PIC 1/7/0 KMD1]iked_pm_ike_conf_request: SA-CFG tunnel-pRBS-cert-TEMP not configured for config payload. Skipping...
[Apr 14 02:26:00 PIC 1/7/0 KMD1]iked_pm_ike_spd_notify_request: Sending Initial contact
[Apr 14 02:26:00 PIC 1/7/0 KMD1]Construction NHTB payload for local:10.185.49.212, remote:10.185.49.194 IKEv2 P1 SA index 1887121709 sa-cfg tunnel-pRBS-cert-TEMP
[Apr 14 02:26:00 PIC 1/7/0 KMD1]Peer router vendor is not Juniper. Not sending NHTB payload for sa-cfg tunnel-pRBS-cert-TEMP, p1_sa=1887121709
[Apr 14 02:26:00 PIC 1/7/0 KMD1]ikev2_packet_allocate: Allocated packet 100f65800 from freelist
[Apr 14 02:26:00 PIC 1/7/0 KMD1]iked_pm_ike_spd_notify_received: Received Unauthenticated notification payload Authentication failed from local:10.185.49.212 remote:10.185.49.194 IKEv2 for P1 SA 1887121709
[Apr 14 02:26:00 PIC 1/7/0 KMD1]ikev2_decode_packet: [100f65800/100fc7800] Received packet: HDR, N(AUTHENTICATION_FAILED)
[Apr 14 02:26:00 PIC 1/7/0 KMD1]ikev2_state_auth_initiator_in: [100f65800/100fc7800] Error: IKE_AUTH packet is missing IDr or AUTH payload
[Apr 14 02:26:00 PIC 1/7/0 KMD1]ikev2_process_notify: [100f65800/100fc7800] Received error notify Authentication failed (24)
[Apr 14 02:26:00 PIC 1/7/0 KMD1]ikev2_state_error: [100f65800/100fc7800] Negotiation failed because of error Authentication failed (24)
[Apr 14 02:26:00 PIC 1/7/0 KMD1]IKE negotiation fail for local:10.185.49.212, remote:10.185.49.194 IKEv2 with status: Authentication failed
[Apr 14 02:25:00 PIC 1/7/0 KMD1] P2 ed info: flags 0xc2, P2 error: Error ok *
********************************
*********************************
pki traceoption
Apr 14 04:32:46 pkid_retrieve_obj_from_lhash, try retrieve obj from lhash type <2> for id <LTEIPsecNEcusRootCA>
Apr 14 04:32:46 pkid_retrieve_obj_from_lhash, error retrieve obj from lhash for id <LTEIPsecNEcusRootCA>
Apr 14 04:32:46 pkid_retrieve_obj_from_lhash, try retrieve obj from lhash type <2> for id <LTEIPsecSEGRootCA>
Apr 14 04:32:46 pkid_retrieve_obj_from_lhash, error retrieve obj from lhash for id <LTEIPsecSEGRootCA>
Apr 14 04:32:46 pkid_retrieve_obj_from_lhash, try retrieve obj from lhash type <2> for id <Ericsson_pRBS>
Apr 14 04:32:46 pkid_retrieve_obj_from_lhash, error retrieve obj from lhash for id <Ericsson_pRBS>
Apr 14 04:35:53 pkid 3 seconds timer off 512 times, pid 1454
Apr 14 04:35:53 pkid 3 seconds timer off 512 times, pid 1454
Apr 14 04:35:54 checkLdapResponse A
pr 14 04:40:11 checkLdapResponse
Apr 14 04:44:26 pkid 3 seconds timer off 512 times, pid 1454
Apr 14 04:44:27 checkLdapResponse
**********************************
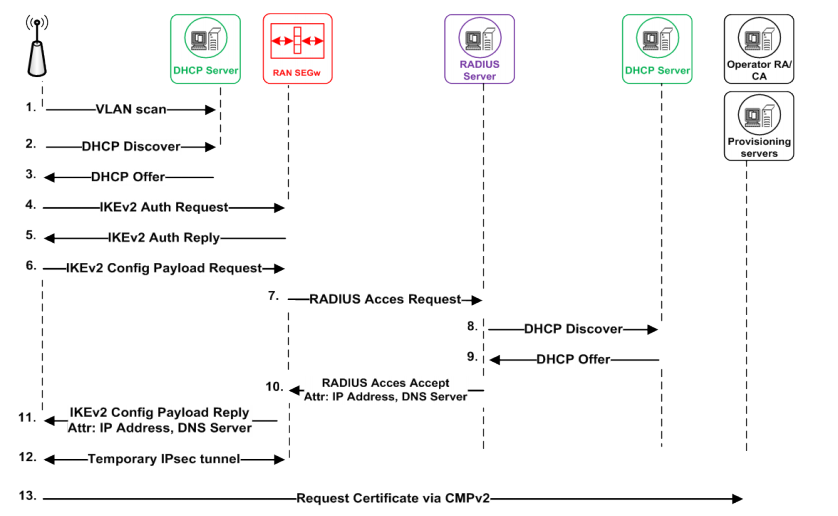
Besides, as show in figure below, when will IKE P1 SA be established? In Step#5 or not until #11?
We have reloaded/renamed CA "EricssonVCRootCA" into "Ericsson_pRBS" in one opperation, so please don't feel confused about it; waiting for your advice and thanks.
Best Regards,
Gavin
#SRX-PKI-IPsec