Hello !
I have compiled and configured such routed-based IPSec. I must say that it is non-standard solution. I have not found a similar in WWW. But I want to know your opinion about this.
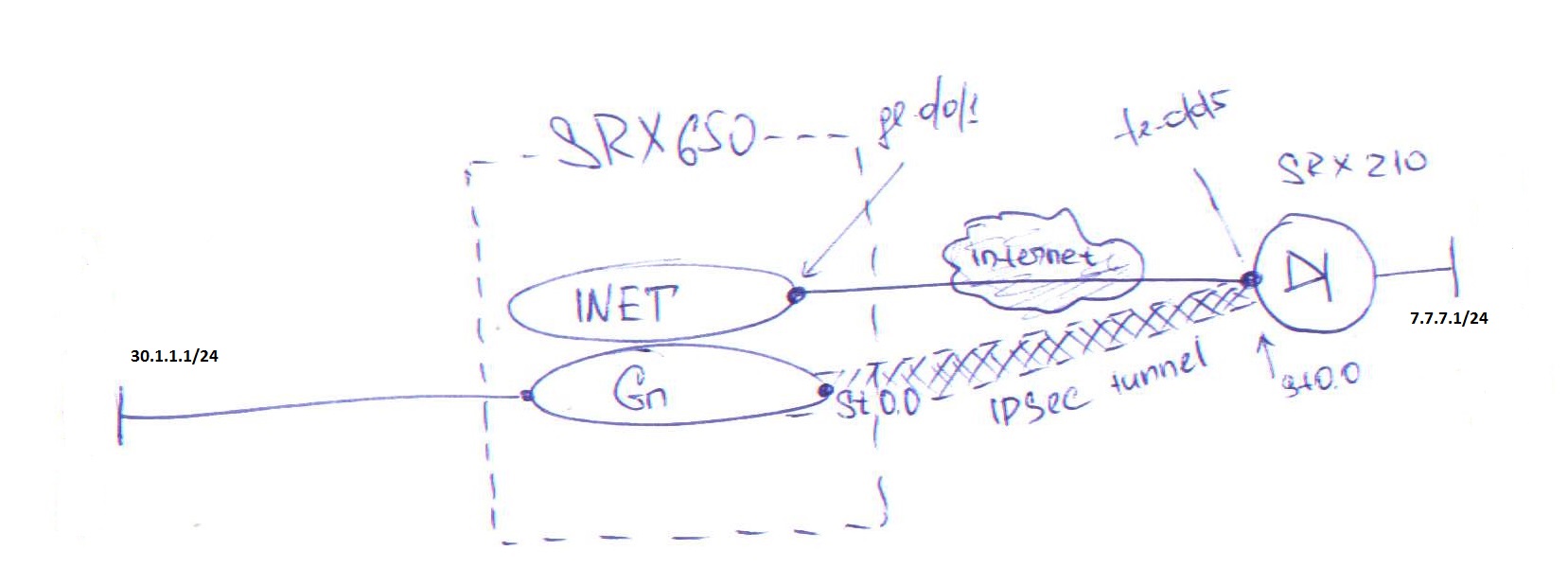
here my goal is:
- To separate the routing and ipsec with different routing-instances. Here routing-instance INET.inet.0 does not know any about network 30.1.1.0/24.
-Link physically connect to INET , vpn interface st0.0 belongs to Gn routing-instance. Gn.inet.0 has route to 30.1.1.0/24( direct).
ICMP packets from source 7.7.7.1 to destination 30.1.1.1 sent and recieved successfully.
Show security ike/ipsec security-associatons outputs say that ike and ipsec is UP.
My question: is scheme correct from the point of view of common sense ?